Security Pre-Assessment (SPA), online Security Self-Assessment (SSA) and Remote Security Validation (RSV) response guide
There may be several different correct solutions to fulfill the requirements in the audit questionnaires. To help you with any questions, we have provided security best practices that we believe can help you to meet the requirements of the TUI Hotel Security Standard. The answers and templates here are only guidelines (it is not necessary to return it to us), and you may have a better and more cost-effective idea of how to reduce your hotel's security risk.Please scroll down on this page to find the guidance for each questions of the security assessments.
RESPONSE GUIDE
Please click on the questions.1. Are the security management processes & mitigation measures documented, reviewed and updated when necessary?
What is a Security Management System?
Security Management System is a formalised, risk-driven framework for integrating security into the daily operations and culture of your Hotel.
It provides the necessary organisational structure, accountabilities, policies and procedures to ensure effective oversight and mitigate risk.
The objectives of a written Security Management System are to:
- Provide, at all times, a safe and enjoyable product to our customers
- Design, develop and implement suitable and proportionate management arrangements, security threat and risk control systems and workplace precautions so far as is reasonably practicable.
- Say how things will be done & what resources will be allocated to achieve them.
- Ensure that, so far as is reasonably practicable, the existing security measures meet at least the baseline standards required by relevant national and international statutory obligations or the additional TUI Group minimum requirements
- Operate & maintain the system whilst also seeking improvement where needed
- Reduce the severity of the impact if something goes wrong and ensure as much as possible has been done towards this – it is recognised that some activities may have an inherent risk.
- Provide a single, consistent, formalised, risk-driven approach to managing security and safety
- To integrate security into the daily operations and culture of your business.
When you should review or update Security Management System?
- Periodically which usually means once a year.
- When the security risk assessment on which Security Management System was built is no longer applicable because the underlying data or information is no longer valid
- Security incidents or “near misses” happened to you or near to you. “Near misses” are events where something went wrong but did not result in injury or damage to property.
- If any of the elements of the Security Management System can be improved
Implementation and maintenance of a complete and thorough system – a security management system
A security management system comprises all security measures, protocols, and procedures part of your Hotel Security. TUI’s external assessor will focus on your management system’s documentation and effectiveness. The hotel’s security management system should be integrated into the overall management of the respective hotel/resort. This means a strong focus is placed upon integrated measures and continuous quality management. Technical/structural, organisational, and personnel provisions should always be considered jointly because they strongly influence each other.
Quality management should be a vital component of every hotel’s/resort’s security management system. All security measures should be clearly planned, implemented, reviewed and adjusted/improved if necessary.
Using external partners such as auditing companies and conducting regular self-assessments can ensure quality management is realised.
If the hotel or resort decides to outsource specific tasks which affect security management, the hotel or resort must retain control over these processes. This requires an explicit agreement to be in place, covering the definition, implementation, and documentation of measures for quality assurance over the outsourced tasks.
The security management system should be documented and reviewed regularly, with updates made where necessary. This documentation should include:
- Security policy is a general statement from the hotel/resort regarding why and how security is being managed
- Risk assessment and risk treatment methodology
- Definition of security roles and responsibilities
- Risk treatment plan
- Inventory of relevant unit assets
- Incident management procedure
- Records of training, skills, experience and qualifications
- Any additional documents which are necessary for ensuring the effective functioning and continuous improvement of the security management system
The Security Management System can be kept in digital or printed format. The most important is that it is accessible to those who need it. Some parts of the security documentation will contain highly confidential information about the business. Hence, restricted access and distribution (internally and externally) should be clarified and guaranteed.
TUI provides a Security Management System Template, which takes you through the main pillars of a management system and holds useful templates that efficiently help you to create the correct documents. Completing the Security Management System Template and following the easy step-by-step To-do’s will have you prepared for Security incidents and a Security Assessment conducted by TUI’s external assessor.
2. Are documented emergency procedures in place and implemented?
Immediate and calm management of an incident is essential to identify the seriousness of the incident, contain the damage and restore operations swiftly. Every hotel/resort should develop and implement special incident handling procedures to successfully diagnose and resolve an incident quickly and effectively. Specific risks identified during the risk assessment process should be factored in when devising incident preparedness procedures.
There are various incident severity levels, ranging from solely suspicious behaviour to near-miss situations and emergencies. Since minor incidents can rapidly evolve into serious emergencies, every hotel/resort should set out clear escalation procedures as part of their incident response process. A functioning incident alert system is essential.
The measures below are designed to introduce and/or enhance existing incident handling processes and procedures to ensure every hotel/resort can promptly respond to and resolve an incident should the need arise.
- Development and maintenance of a key contact list and implementation of a contact management protocol – (For more details, please go to: Are emergency contact details (police, fire brigade, hospital, regulatory authority etc.) provided and kept easily accessible?)
- Preparation of communication lines and public communication systems – ensuring they are easily accessible for customers – introducing processes to alert, alarm and respond in case of an incident – (For more details, please go to: Are emergency communication lines (alerting, alarming, response procedures & measures) implemented in-house such as PA system or loudhailer/megaphone?)
- Introduction of a process for incident reporting and investigation – (For more details, please go to: Are processes or systems in place to inform TUI or its representatives in case of any security occurrences that impact customer security?)
3. Are emergency contact details (police, fire brigade, hospital, regulatory authority etc.) provided and kept easily accessible?
Develop and maintain a key contact list, and implement a contact management protocol
Reaching the right people at the right moment is key to effectively responding to an incident. Hence, every hotel/resort should have a key contact list and contact management protocol that is documented, readily available to all staff members and regularly updated. A non-exhaustive contact list of external and internal stakeholders includes:
- Internal functions (e.g. management, security personnel, maintenance team, customer services, all staff)
- State agencies, public services, local authorities and response forces (e.g. police, ambulance/hospitals, HAZMAT* response teams, supervisory authorities)
- Neighbouring properties/facilities which might need to be alerted in case of an incident
- TUI functions (e.g. TUI MM, Group Product & Purchasing)
- Suppliers/contractors and external experts (e.g. transport providers, tour operators, booking agents, insurance companies, alternative accommodation, psychological support services)
- Media
The key contact list should be included in the hotel’s/resort’s security plan. All staff members should be made aware of emergency contacts (e.g. in case of identified suspicious behaviour). The contact list should be available in digital and paper form and stored securely. Back up in both digital and paper form is required.
The security personnel responsible for communicating with external parties should be formally assigned and authorised to do so by the hotel’s/resort’s management. Designated personnel should engage with external stakeholders regularly and maintain open communication channels. For example, local police/fire/emergency services should be familiar with the hotel’s/resort facilities to efficiently and effectively respond in an emergency.
4. Are emergency communication lines (alerting, alarming, response procedures & measures) implemented in-house such as PA system or loudhailer/megaphone?
Prepare communication lines and public communication systems – ensuring they are easily accessible for customers – introducing processes to alert, alarm and respond in case of an incident
In case of an incident, every hotel/resort should develop and implement the alert/alarm/respond process. The process should be documented and readily available to all employees.
The process should be reviewed regularly and updated when necessary to address newly assessed risks. All hotel/resort employees should receive regular training. Drills should be conducted frequently.
Every staff member should be made aware of the 24/7 security focal point person to report any incident or suspicious behaviour. Hotel/resort guests should also be informed of the presence of the 24/7 security focal point person and should be asked to report any incident or suspicious activity immediately. Moreover, guests should be prompted to familiarise themselves with the hotel’s/resort’s special procedures about how to behave in specific incidents such as in the event of an evacuation.
This information should be readily available in all hotel/resort guest rooms and in designated common areas. This information should also be accessible through the hotel’s/resort website and mobile apps.
For immediate alerting in case of an incident, it is strongly recommended that emergency phones are easily visible and accessible to all in designated common areas (e.g. lobby, pool area, bar, cash handling areas, guardhouses, highly crowded or remote locations). In addition, discrete panic buttons for staff members are also recommended.
The 24/7 focal point person should be adequately staffed with competent personnel who are able and authorised to initiate response measures and deploy escalation procedures when needed. The hotel’s/resort’s alert system should be easily and clearly located and should be accessible to the 24/7 focal point person at all times.
Incident response requires communicating to different stakeholders based on the type and scale of the incident. Hence, an individual, as well as a collective, and a stakeholder communication plan should be available (e.g. provision of call circuits and apps with different distribution lists/groups).
A functioning public announcement system (e.g. loudspeakers, light signals, sirens) should be in place and cover all areas so that all people on the hotel’s/resort’s premises can be alerted in case of an incident. Announcement scripts for specific scenarios (e.g. fire, evacuation) should be prepared in advance and be made available to all staff members without delay. The announcements should be clear, understandable, loud enough, and available in the main languages spoken by staff and guests. The use of code words, which are well known to the staff and trigger particular staff behaviour, should be considered.
For alerting and alarming purposes as well as for ongoing communication between the hotel’s/resort’s security functions, backup technical communication solutions should be available. This means that the hotel/resort cannot solely rely on, e.g. mobile phones or online services to communicate in case of an incident. Alternative channels (e.g. radios, personal communication chains) are needed in case the traditional communication channels fail. Power cuts should also be considered, and an appropriate backup power supply for critical devices (e.g. server room, emergency lighting) should be installed. Moreover, depending on the hotel’s/resort’s location, the existence and maintenance of a satellite communication device should also be considered.
5. Are processes or systems in place to inform TUI or its representatives in case of any security occurrences that impact customer security?
Introduce process for incident reporting and investigation
Every hotel/resort should have formalised incident reporting and investigation procedures. This should include consistent and detailed recording of all incidents, people involved, measures taken, and, if applicable, lessons learned and the involvement of local authorities. Crimes should be reported to the local authorities immediately and at all times. Moreover, major incidents and significant security trends/developments should be communicated to TUI.
When escalating a major incident or significant security trend to TUI, please contact your local TUI representatives
Appropriate procedures should be in place to ensure an incident minimally impacts the hotel/resort and swiftly restore normal operations. All staff members should be trained on these procedures, and drills should be conducted regularly. A review of these procedures is needed if circumstances change.
6. Is there a periodic risk assessment conducted that documents foreseeable risks in all areas including physical, personnel, and information security?
How do you manage your risks?
- Step one – Risk Assessment.
- Identify all the risks
- Select the risks that are not acceptable
- Step two – Risk Treatment Plan
- Give one or more options for treating each unacceptable risk
- Choose between the available treatment option/security controls and/or other activities to lower risk to an acceptable level
- Assign who is responsible for the implementation
- Assign deadlines
- Assign resources (i.e., financial and human) that are required for the implementation
- Decide how you will evaluate if the implementation was done correctly
Step One – Risk assessment
Conduct regular risk assessments to identify and evaluate existing risks
Many companies make their first mistake by starting implementing the risk assessment without deciding the methodology they will use. It may sound complicated at first, but imagine beginning to build a house without any clear rules on how to do it. The best thing is to lay the guidelines/rules on the whole risk assessment process in a document for your reference. You will have to define your methods in the following areas/elements:
1 – How will you identify the risks that could cause the loss of your assets?
2 – How will you identify the risk owners?
3 – What will be the criteria for assessing consequences and the likelihood of the risk?
4 – How will you calculate the risk?
5 – What are the criteria for accepting risks?
If you answer these questions, your risk assessment will be consistent and comparable year to year or between units if you own more hotels.
How will you identify the risks that could cause the loss of your assets?
One methodology to identify risk is to use the assets, threats and vulnerabilities method, but you can approach risk assessment based on different methodologies. Another methodology is the “Process Method”, where you analyse a sequence of steps or interactions of activities and processes based on risk sources, departments, objectives etc… Whatever methodology you choose needs to be simple as possible and should contain these five elements mentioned above. Copying and using a methodology from other hotels, especially if it is a bigger one, makes you just do risk assessment and treatment for a long time instead of finishing it just in a couple of days.
How will you identify the risk owners?
For each risk, you need to find the person interested in solving the risk and is in a high enough position to solve the problem if it arises.
What will be the criteria for assessing consequences and the likelihood of the risk?
Consequences and likelihood should be assessed separately for each of your risks. You can use numbers or simple low-medium-high scales. We recommend that you describe the conditions to be met for each scale as precisely as possible, thus ensuring consistency.
How will you calculate the risk?
You can do it by multiplying or adding the numbers. In case you used the low – medium-high scale, that could be equivalent to 1-2-3 on a scale. The result gives you the relative importance of each risk and helps you to prioritise your effort by sorting the risks by the risk value.
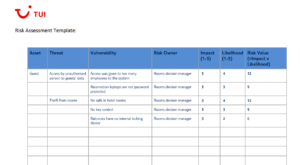
Click here to download the template
What are the criteria for accepting risks?
Whatever numerical risk calculation method you choose will produce a scale (e.g. 1-25). Once you know how to calculate risk, you will need to decide above which figure you will need some action on. E.g. you decide the acceptable risk level is 16, any risk valued above that number needs to be treated. If you don’t want to use a numeric scale, you can decide whether you need to treat a threat or not based on your own experience and insight.
Tips:
- First, find the methodology that best fits your circumstances
- The method you choose should contain the five elements mentioned above
- Find the right people and involve them in the risk assessment process. Department Heads will know best any potential security problems.
- It is not going to be perfect at first. It is better to do a simplified, less detailed risk assessment first, to which you can return later to review, add or modify certain risks than to spend too much time on the risk assessment.
Step Two – Risk treatment plan
The risk treatment aims to establish how you will control the unacceptable risks identified during the risk assessment
You should focus in this phase only on risks that are not acceptable, and you will have to take into account the available budget for your current year too. Risk scoring (if you used one in the risk assessment phase) will help you to prioritize between risks.
Treatment options
The options you have to treat a risk are:
- Risk avoidance– In case the risk is too big to mitigate with any other options you may decide to stop that particular activity – e.g., there is a clear and present danger of a terrorist attack you may evacuate a hotel and stop providing accommodation services
- Risk limitation– This includes the implementation of different safeguards or control measures. – e.g., Using armed guards, metal detectors or simply including safes in the rooms to avoid theft. Normally this solution is the most common.
- Risk transference – You transfer the risk to another party – e.g., normally that means you buy an insurance policy. This option does not have any effect on the threat itself, therefore the best is to use risk-sharing with options a. or b. combined.
- Risk assumption– That means you accept the risk without doing anything about it. This option normally is used only when the mitigation costs would be a lot higher than the damage if an incident would occur.
Options for security controls
The main types of control elements are:
- Operational elements: organizational structure, security guard staffing, and rules are documented through plans, policies, procedures, instructions, administration of delivery processing, training, visitor control, incident responses, emergency response etc.
- Architectural elements: layout, barriers, locks, exterior and interior lighting, parking layout, critical building services etc.
- Security systems elements: intrusion detection and alarm systems, automated access control systems, closed-circuit television (CCTV) systems, security control centre equipment, communication systems
Selecting control measures
- As we mentioned earlier it is not practical to address all identified risks. You should give priority to those ones in the asset–threat and vulnerability pairs that have the most potential to cause harm to you.
- Here is where you have to consider your available budget for the current year because some of the controls may have a cost or require an investment.
- When you create your risk treatment list the best to involve only those who are the experts on the specific treatment option. E.g.: if it is about the employer screening it belongs to Human Resources typically or for an IP-based CCTV system you involve your security expert, you may also involve an external specialist and your IT department.
- After considering all the above-mentioned points you will have to choose between the available treatment options/security controls and/or other activities
- The Risk Treatment Plan is the implementation plan of your chosen risk control strategy. You will have to decide who is responsible for the implementation, what are the deadlines and which resources (i.e. human, financial) are necessary. You will have to include in the plan also, how you will evaluate the implementation
- In the end, you will have to seek authorization from your appropriate management level and start with the implementation
Example of risk treatment planning template :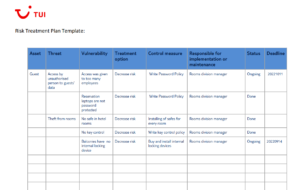
7. Are you continuously monitoring external risks, such as protests etc., by using local media and government agencies to keep yourself informed?
Perform dynamic, ongoing risk assessment / situational awareness to continuously update the initial risk assessment.
The difference between a formal risk assessment is that they are prepared in advance, recorded, and monitored regularly. Conversely, dynamic risk assessments are ‘dynamic’ or ever-changing and carried out on the spot by an individual when they enter a new environment or their current environmental changes.
This requirement has two elements:
- First, be aware of one’s surroundings and identify potential threats and dangerous situations
- Second to continuously assess potential threats and dangerous situations and take action to eliminate or reduce risk
Situational awareness
It is essential, not just for personal security but as a fundamental building block in collective security.
It is important to note also that situational awareness — being aware of one’s surroundings and identifying potential threats and dangerous situations — is more of a mindset than a hard skill. Situational awareness is crucial for recognising terrorist threats, but it also identifies criminal behaviour and other dangerous situations.
The primary element in establishing this mindset is first to recognise that threats exist.
A second important element of the proper mindset is understanding the need to take responsibility for one’s own and others’ security.
The discipline part of practising situational awareness also refers to the conscious effort required to pay attention to gut feelings and surrounding events even while being busy and occupied by other operations. Security awareness is an ongoing state of mind that incorporates a security perspective into your daily activities.
Dynamic Risk Assessment
After identifying potential threats or dangerous situations, one should continuously assess the risk, take action to eliminate or reduce risk, and monitor and review the rapidly changing circumstances of an operational incident.
What does it mean in real life? Situational awareness and dynamic risk assessment is one process that we are all likely to do unconsciously throughout the day. For example, you walk home at night and see a group of people standing in a poorly illuminated corner. You recognise the hazard; you decide to pass by them or choose another route. This requirement should be practised on every level in a hotel environment. It could mean, for example, that a manager reviews the newspapers daily, listen to local news channels and looks for any signs of social unrest. Another example is that an employee recognises that somebody is doing surveillance/hostile reconnaissance at the hotel or a suspicious item is left in the lobby and takes action.
Click here for more info on “situational awareness” & “dynamic risk assessment.”
8. Is there a person responsible for the security management of the hotel?
Security Responsible Person
A security responsible person (SRP) should be designated to manage directly or indirectly security tasks. The SRP should be responsible for ensuring the deployment of the security management system and should regularly report to the hotel/resort management on the system’s effectiveness and efficiency, immediately flagging any concerns to the hotel’s/resort’s management. SRP is typically represented by a manager. Sometimes, especially in smaller hotels, their main role within the hotel may be something other than security.
The responsibilities of a Security Responsible Person include, but are not limited to, the following:
- Conducting & reviewing the security management system
- Ensure there is a security training program
- Report regularly on the system’s effectiveness and efficiency as well as flag any concerns to the hotel’s senior management
See also “Are security resources with clearly defined responsibilities allocated?”
9. Are security resources with clearly defined responsibilities allocated?
Security requires 24/7 monitoring, which usually implies shift schedules. These should be recorded (planned and actual) and, if applicable, also include rosters for detection/watchdogs according to the length of their deployability so that the relevant person/people can be identified in the event of an incident or investigation.
Where it is applicable (when a risk assessment identifies the need for security personnel), the visibility of security personnel can provide reassurance to the guests and make their stay even more enjoyable. However, appropriate and neat dressing is essential, creating a positive perception of the security personnel. Security staff must also be friendly and approachable in case of guest enquiry. Moreover, the security personnel should be equipped adequately to perform their duties correctly.
The 24/7 security point of contact
Security incidents can be diverse and happen at any time of the day or night. It’s essential to have one person that is the first point of contact for any security incident 24/7. The front desk can efficiently serve as the first point of contact depending on the risk assessment. They can then contact the individual with overall responsibility dependent on the level of authority you give them or the nature of the incident.
- Make sure that your staff are regularly trained to respond to a security incident.
- Ensure that staff and guests know how to contact the 24/7 point of contact in a security incident
- Also, think about the necessary authority that your front desk staff need to be given to fulfil their duty as a security point of contact (e.g. do they have the authority to call the police?).
Different roles & responsibilities in your hotel:
Security is everyone’s responsibility. The hotel/resort should review who else within its team has or could have security responsibilities. It must be ensured that staff is aware of their responsibility, they are trained and have the necessary tools and authority to respond to a security incident. Here’re some examples of possible roles and responsibilities:
Front Desk:
- Access control, e.g. key cards, wristbands, left luggage.
- Regularly trained on potentially fraudulent activities involving credit cards, currency exchange etc.
- Serve as a 24/7 security point of contact (see above)
Bar Manager or Head Bartender:
- Observing suspicious activities, objects, and people within the bar area.
- Ensuring that all stock is accounted for regularly.
- Is fully trained in how to record and store/transport the takings at the end of the day or shift.
Housekeeping:
- The Head of Housekeeping has an accurate record of the allocation and return of Master Key Cards.
- Cleaning supplies are stored in a lockable location, and stock taking is conducted regularly.
- Trained in observing suspicious activities, objects, and people during their housekeeping activities.
Kids Club/care Manager or Supervisor:
- Fully conversant in missing child protocols and escalation to senior management.
- Maintain and challenge the sign-in and out process of children attending the club.
- A regular check of the Club perimeter and access points, ensuring locks and any CCTV are positioned appropriately.
Restaurant Manager
- Observing suspicious activities, objects, and people when in the restaurant
Maintenance Team:
- Prioritizes security issues, e.g. doors or windows not locking.
- CCTV cameras are kept free of foliage and debris, and all are recording correctly.
- Perimeter is maintained, and any repairs are conducted as quickly as possible.
Giving authority
Once personnel is appointed to a security task, they must be empowered and trained to have the confidence and the knowledge to do what is required of them when the situation arises. For example, maintenance is required to report any damage to the perimeter. If they come to the management with a concern, the manager should invest the time to look at the issue and resolve it jointly. This will encourage good security behaviours and keep employees motivated.
See also “Is a member of staff nominated as responsible for security?”
10. Is there a security training system to educate newcomers, update existing staff with knowledge and skills, and/or train employees on emerging incidents?
Once relevant security measures have been identified, it is vital staff are thoroughly trained on all security procedures to ensure accurate implementation and monitoring. Security training should be incorporated into organisational training practices. This program should cover the training of the newcomers, update existing knowledge and skills, or train employees on new hazards. The training program should comply with all applicable international, national and local laws and regulations. It should also consider any further training needs identified by your risk assessment.
Conduct employee training
Security training and drills should take place with all staff according to their tasks and should be documented accordingly. All staff should be briefed on their role regarding security and the actions to be taken in case of an incident – to protect themselves, guests, and the hotel/resort. Real-life scenarios should be simulated and trained for through comprehensive drills. External parties such as state security forces, emergency services, and neighbouring stakeholders should be included in such exercises to improve overall cooperation.
Develop a security culture
All staff members should be encouraged to become involved in the security management of the site. This means they should understand the hotel’s/resort’s security approach and existing risks and how these can be encountered in their respective working environments.

